
Traditionally, control system networks were based on proprietary protocols and infrastructure. While cost and complexity were detrimental factors, the advantage of these systems was an inherent level of security not provided by contemporary control communication architectures.
Interoperability and information exchange between business and control systems has become increasingly important as ERP and MES systems marry the business and control environments. Unfortunately the easiest way to facilitate this information exchange is to ensure that there are no intervening devices that can derail communication. The result: a convenient, but high risk sharing of infrastructure. Control systems are now unintentionally exposed to the Internet, and a greater amount of unauthorised access, simply because the sharing of infrastructure makes physical access control much more difficult.
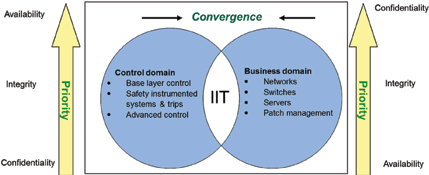
The question may be asked, “But what makes control networks different?” The answer to this can be surprisingly complex, but in essence the requirements or ‘objectives’ are very different. Figure 1 shows that while there is a certain amount of convergence, priorities are fundamentally different.
What must be done to separate and secure your control networks?
Have a limited number of access points between the business and control networks: preferably there should only be one connection in a physically secured area. This is not always possible, but the number must be as small as possible.
Implement firewalled DMZs or unidirectional data gateways as part of the access point(s): losing the connection or protecting firewalls to an attack should allow one to physically disconnect and isolate the control network to allow continued integrity and operation of the control system.
Unplug the Internet: the biggest threat faced by owners of control systems is direct access to equipment from the Internet. This is ably illustrated by Shodan (www.shodanhq.com). The most frequent objection to this is that remote access is required. Probably the safest solution, although it is not perfect, is to make use of VPN access with the VPN forming part of the firewall.
Check for intrusion: very few control networks are equipped with intrusion detection systems. The fact is control systems will experience unexplained problems and outages and in some (hopefully relatively few) cases it will be due to system intrusion. The problem is however, if you do not monitor for it, you will most likely never know your systems have been penetrated.
Get rid of dual zoned equipment: people using one machine for business and process will almost never consider the impact of having one machine with direct access to both networks. Even if only one machine like this exists on the network, it invalidates all firewall separation because it provides a direct alternative route to the control network. Many of the inadvertent Internet exposures take place in this manner.
In conclusion, it is critical to separate control and business networks as the security problems can have dire consequences. The one aspect that is frequently ignored is that it must be a managed, controlled and monitored process, just like quality or safety management.
For more information contact Cobus Pool, Proconics, +27 (0)17 620 9725, [email protected], www.proconics.co.za
| Tel: | +27 11 568 4780 |
| Email: | [email protected] |
| www: | www.proconics.co.za |
| Articles: | More information and articles about Proconics |

© Technews Publishing (Pty) Ltd | All Rights Reserved