
The bidirectional flow of information between business IT and manufacturing IT is critical to real-time decision-making at all levels but presents its own set of problems regarding security. The owners of these networks are naturally wary of providing access to information and functionality which could prove dangerous in the wrong hands.
Background
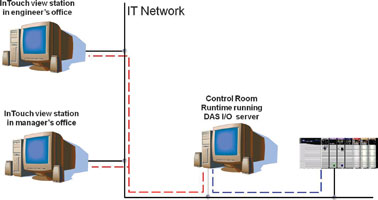
Lonmin’s original IT network had a flat topology with a DAS I/O server collecting data from the PLCs and communicating this to view stations for the shift boss, mine captain or engineer (Figure 1). But, in order to conform with security policies, it was decided to separate the control network from the IT network which resulted in the topology shown in Figure 2 where the production and control networks are two VLANS running on one control domain separate from the IT domain. The production and control networks are present in the control rooms, process plant and in the production areas but not in the office areas.

This arrangement, however, disconnected the shift boss, mine captain and engineer from the scada system and they lost the ability to view production information in real-time. To address the problem, a DMZ (demilitarised zone) was implemented. A DMZ is a network that serves as a buffer between a secure protected network (control network) and an insecure client network (IT network). A DMZ usually contains servers which provide services to users from the client network, such as the web and, in this case, terminal services. These servers are open to limited access from the client network, but protected by a firewall.
But this brought with it the issue of how to deal with security because office personnel could not be allowed unqualified access to the control systems. One way around this was to deploy additional view stations on the control domain only by extending the network and its infrastructure (equipment, fibre links, PCs, etc,) but this would prove costly per view station and would also require time to implement.
The challenge therefore, was how to provide the office area with plant information in real-time while conforming with all security policies and at minimum cost.
Selecting the solution
Three approaches were considered. The first was to use ArchestrA read-only view stations, but this would incur the additional network infrastructure costs just mentioned and require the ability to maintain multiple applications.
“The second option was to make use of the Wonderware Information Server,” says Johan Louw, automation specialist, Lonmin. “Although Information Server allows access from any network PC, this was a real-time scada reporting environment which this solution supports but which is better served by the third option which was the use of Terminal Server.”
Terminal Server, which supports Microsoft’s Remote PC Connection, provided Lonmin with a list of features that met its specified requirements with a remarkable degree of accuracy and which included:
* No Wonderware installation required – this allowed Lonmin to be self-sufficient.
* Quick implementation – “Where some engineers expected me to be busy for an hour or more, I was finished in a matter of two to three minutes,” says Louw.
* Easy access and security control – all access to the system is controlled from one server and this allows the full control of where scada access is available and also provides for the instantaneous granting or withdrawal of access rights to individuals. It was previously impossible to know who had access to which scada system or if this access was permitted.
* Easy application maintenance – all applications are maintained and updated at a central location without the need for deployment to a multitude of workstations.
<i.* Multiple applications hosted on one server</i> – all of Lonmin’s multiple mine shafts, each with its own scada system and applications can be hosted on a single server thereby providing convenient access to those who need it.
* Client can view multiple applications at once – terminals are not dedicated to any single application and can switch between applications at will.
Implementation
The first step was to set up Terminal Server and to install the InTouch HMI/scada application. “The read-only version prevents any user from changing/stopping or starting any equipment on the scada. We then deployed the System Platform and its view engine as well as all the applications,” says Louw. “The next step was to define user access and their sessions which involved specifying which applications each user can access. Thereafter, the only thing left to do was to set up remote access to the server – something which is really quick to do.”
Applications start automatically when selected but server access beyond the permitted range of applications is prohibited thereby preventing any wilful or inadvertent damage to the system. The application run time can also be specified so that if a shift boss or engineer forgets to sign off from the application, it will self-terminate in the specified time period. This feature also lessens the network and server loads.
The System Platform’s Integrated Development Environment shows which platform and view engine is in use as well as changes to any software releases. New software releases can then be deployed to all remote users instantly.
Benefits
* Real-time process information is available in the office to support informed decision-making.
* Independence of IT and production networks while providing a secure access from one to the other.
* Easy and secure end-user access to multiple applications.
* No interference with scada system operation possible.
* Greatly reduced software support, maintenance and deployment costs.
* High system speed and minimal network loading.
For more information contact Deon van Aardt, Wonderware Southern Africa, 0861 WONDER, [email protected], www.wonderware.co.za

© Technews Publishing (Pty) Ltd | All Rights Reserved