
Cyber attacks against critical network infrastructure can have severe consequences ranging from operational shutdowns, to damaged equipment, financial loss, and even theft of confidential information. The imminent concern has put world governments on high alert.
The U.S. Department of Homeland Security (DHS) has grown weary over the growing number of cyber attacks on industrial control networks. To provide clear cybersecurity guidance to organisations implementing the IIoT, the DHS published guidelines to ‘provide a strategic focus on security and enhance the trust framework that underpins the IoT ecosystem’. Among the measures discussed are ‘considered connectivity’ and ‘defence in depth’.
Enforcing data privacy and security procedures
IIoT ecosystems need to aggressively enforce cybersecurity strategies for personal as well as third-party networks. Recent security procedures from the following companies have fallen short of good practice, putting millions of people at risk.
In 2016, hackers used stolen credentials to gain remote access to the Ukrainian power grid and cut power to 30 substations, affecting 225 000 customers. The hackers even installed custom firmware, deleted master boot records, and shut down telephone communications.
Another major IIoT attack occurred when hackers breached Target’s network by using malware to penetrate a HVAC company that was working for them. Personal data from over 100 million customers was stolen.
With the rising popularity of connected cars, new vulnerabilities also arise. In 2015, researchers were able to imitate BMW servers and send remote unlocking instructions to vehicles. Jeep also failed security inspections when researchers were able to remotely access vehicles and control everything from the GPS, to steering, to brakes and even engine control. Consequently, 1,5 million Jeep vehicles were recalled.
Defence in depth for IIoT organisations
IIoT organisations are advised to adopt a defence in depth approach to help them stay ahead of privacy and security risks. Organisations must have a complete understanding of the function and scope of each individual device. If not, organisations run the risk of activating direct connections to the Internet when they are not needed.
Next, organisations must make a conscious decision about every IIoT connection. At times, connecting to a local network to allow the content of critical information to be analysed before it is sent is sufficient. Industrial control systems (ICS) are complex and critical. It is essential to protect them using defence in depth principles.
Additionally, organisations must build-in remote management capability. Manufacturers, critical network infrastructures and service providers must be able to disable network connections or specific ports remotely when needed.
Managed VPNs for remote connectivity
IIoT systems are highly attractive to cybercriminals who regard them as the most vulnerable point in the network. Protection of remote connections on IIoT systems is best managed with VPN (virtual private network) software.
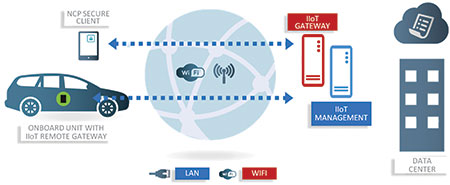
VPNs form a secure connection at the remote IIoT gateway, integrating seamlessly with existing infrastructure and encrypting all data traffic passing to and from individual devices. With VPNs, device patching, updating, authentication and connectivity can all be managed remotely, which minimises any potential threat of a cyber attack.
All IIoT devices accessing a network should have up-to-date firmware and implement network security technologies, such as intrusion prevention systems (IPS) and firewalls along with VPN software.
Not only does VPN software integrate easily with existing corporate systems, it also secures data traffic at device-level. This ensures information stays encrypted and private as it passes between cloud applications, IIoT and mobile devices that access them.
Overall, the issue of IIoT or machine-to-machine (M2M) security is primarily focused on organisations taking adequate precautions to manage and protect data privacy.
To achieve defence in depth, IIoT organisations must re-evaluate on-demand/always-on access, along with command line or API control. In addition, authentication in the form of software/hardware network certification and central management for remotely configuring devices are vital.
By frequently reviewing network connections, securing every remote connection with VPN management, and ensuring IT operatives follow in depth privacy and security practices, companies will be able to mitigate cybersecurity threats.
More ARC Advisory Group’s Industrie 4.0 Viewpoints can be found at https://industrial-iot.com
For more information contact Paul Miller, ARC Advisory Group, +1 781 471 1141, [email protected], www.arcweb.com

© Technews Publishing (Pty) Ltd | All Rights Reserved